Proactive Threat Hunting: Techniques to Identify Malicious Infrastructure
Learn how to hunt malicious infrastructure using SSL certs, favicons, HTTP headers, JARM, and IoT search engines like Netlas, Shodan, and Censys.
March 17, 2026
→
Top 10 Hacking Devices for Ethical Hackers in 2026
Explore top hardware pentesting tools (Flipper Zero, Rubber Ducky, WiFi Pineapple, Proxmark3, HackRF) with real-world cases
February 6, 2026
→
Inside ClickFix: How Fake Prompts Took Over the Web
ClickFix turns fake CAPTCHAs into user-executed malware chains. Learn how campaigns evolve, how to hunt them at scale with Netlas, and how to stop them
January 30, 2026
→

Nmap Cheat Sheet: Top 10 Scan Techiques
A practical cheat sheet explaining the top 10 Nmap scan techniques — how they work, when to use them, and how to configure scan scope, speed, and output.
June 19, 2025
→
Google Dorking in Cybersecurity: Techniques for OSINT & Pentesting
Explore Google dorking techniques to boost your OSINT and penetration testing. Learn automation tricks, best practices, and top analogues.
June 16, 2025
→
DNS History: Exploring Domains Past by Inspecting DNS Trails
Discover how historical DNS records reveal domain changes, security trends, and competitive insights to strengthen your online presence.
June 11, 2025
→
Important Updates, Sales & Promos
Email newsletterOnce a month
Please, sign in to manage newsletter subscription

Netlas vs Urlscan: Tools Comparison
At first glance, Netlas and Urlscan seem similar, but their core functions and use cases differ greatly. Discover which tool fits your needs.
June 5, 2025
→
Netlas vs IPinfo: Tools Comparison
Explore the features, strengths, pricing, and automation options of Netlas and IPinfo to choose the best IP intelligence tool for your cybersecurity or research needs.
May 20, 2025
→
Netlas vs ZoomEye: Platforms Comparison
Compare IoT search engines Netlas and Zoomeye, highlighting their features, strengths, and ideal use cases for security research.
March 21, 2025
→

Using Uncover with Netlas.io module
Instructions for using the Netlas module integrated into Uncover from ProjectDiscovery
March 13, 2026
→
Using Subfinder with Netlas Module
Instructions for using the Netlas module integrated into Subfinder from ProjectDiscovery.
February 7, 2025
→
Netlas Chrome and Firefox Extensions
The article is devoted to installing and using Netlas browser plugins for Chrome and Firefox.
February 5, 2025
→
All posts

March 20, 2026
How we hunt C2 infrastructure at RST Cloud using Netlas

March 17, 2026
Proactive Threat Hunting: Techniques to Identify Malicious Infrastructure

March 13, 2026
Using Uncover with Netlas.io module

March 6, 2026
Netlas Updates Terms and API & Data License Agreement

February 6, 2026
Top 10 Hacking Devices for Ethical Hackers in 2026

January 30, 2026
Inside ClickFix: How Fake Prompts Took Over the Web

January 23, 2026
Top 10 Critical Threat Actors to Watch in 2026: Ransomware, APTs & Defensive Strategies

January 16, 2026
Bug Bounty 101 - A Complete Bug Bounty Roadmap for Beginners (2026)

December 26, 2025
Supply Chain Attack - How Attackers Weaponize Software Supply Chains

December 15, 2025
LLM Vulnerabilities: Why AI Models Are the Next Big Attack Surface

December 12, 2025
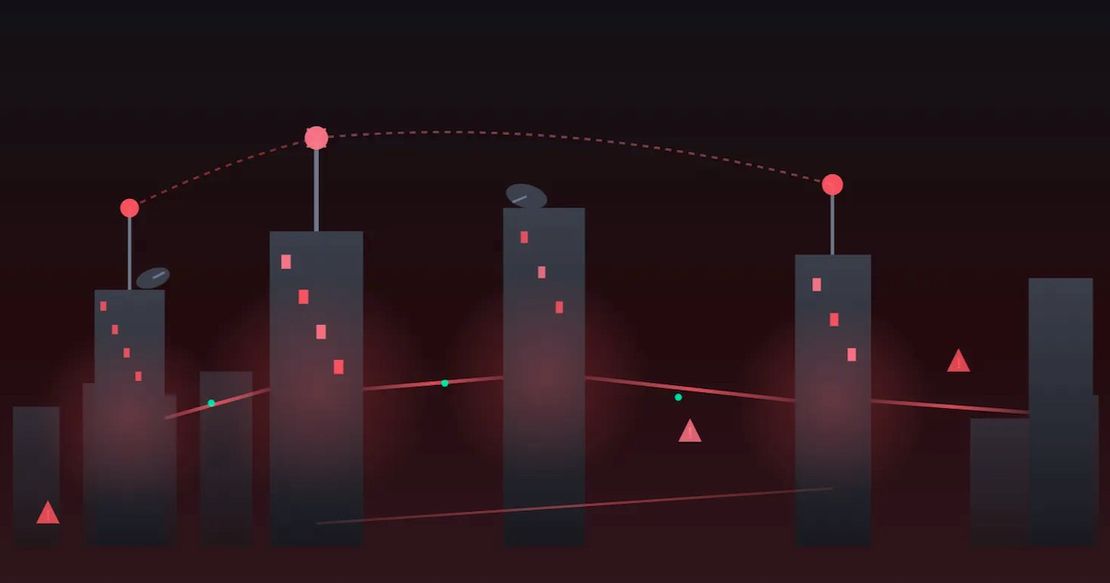
The Evolution of C2: Centralized to On-Chain

November 21, 2025
From Starlink to Star Wars - The Real Cyber Threats in Space