Netlas provide visibility into devices and services exposed to the internet. This data allows for effective use of the search engine within threat hunting, primarily for identifying infrastructure owned by malicious actors.
Utilizing Netlas, a threat hunter can quickly identify IOCs (Indicators of compromise) of a specific malicious software, search for other instances of such software using IOCs as a search patterns, and promptly stop interaction with malicious infrastructure.
An example of IOCs and search query for open-source phishing framework is given in another case concerning IP reputation scoring. Another great example is the search for malicious servers.
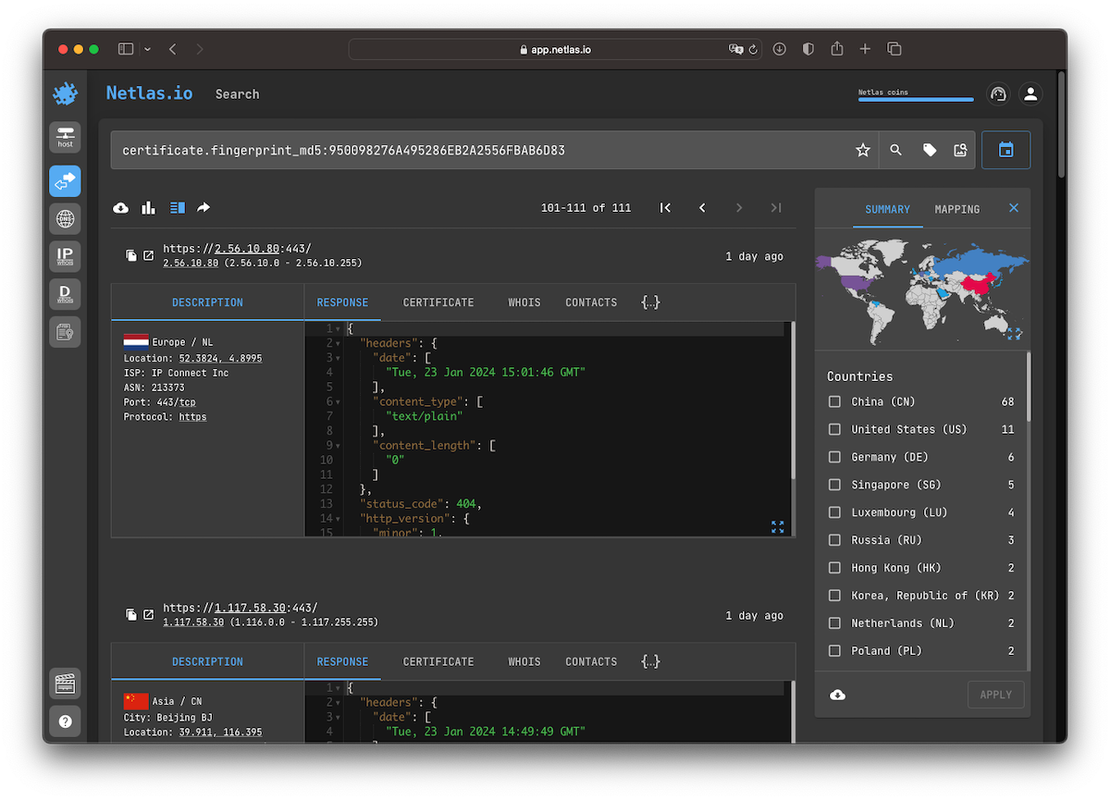
Search for C&C servers
Command and Control (C&C) servers employed by malicious actors to control infected computers, typically hide or masquerade as something legitimate. Researchers need to consider various factors and their combinations to create search pattern. Possible indicators include:
- fields in the service response headers;
- title and content of the returned web page (for web);
- favicon (for web);
- used ports and protocols;
- SSL certificate and secure connection settings;
- specific error codes or error messages, etc.
Search by SSL certificates is often the most effective. Since certificates are not issued for each instance separately, their match indicates the use of the same software. Verification can be done based on JARM fingerprint for TLS and hashes for SSL. Using this approach, you can find, for example, Metasploit servers or or Cobalt Strike software. In addition to hashes and fingerprints, the search can be carried out using fields such as subject, issuer, and so on.
All the features mentioned above are available for search on Netlas. By identifying several IOCs and assessing the significance of each, the researcher can create a search query that will identify C&C servers using Netlas.
Similarly, services used for penetration testing, frameworks for emulation or execution of attacks, sites infected with crypto-miners, and much more can be found.
Other threats and exposed systems
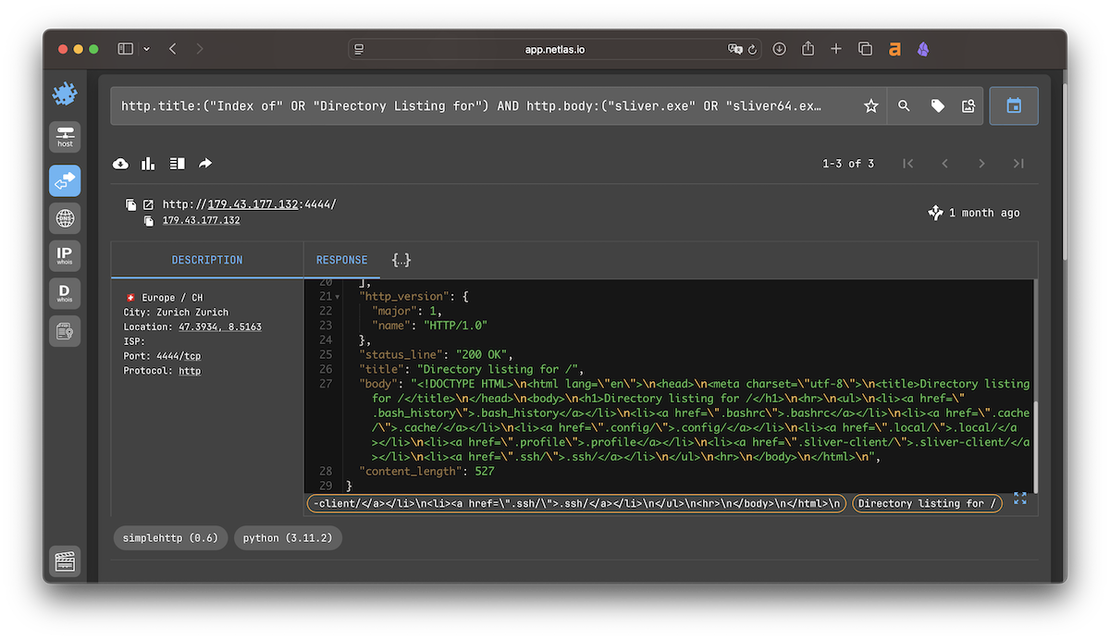
Netlas can also be used to find malware staging servers that host implants, loaders, and post-exploitation tools. One practical example is the search for open directories exposing Sliver-related payloads and client files.
Additional materials
For more threat hunting and threat intelligence examples, see the related materials below and explore articles tagged with Threat Intelligence →.